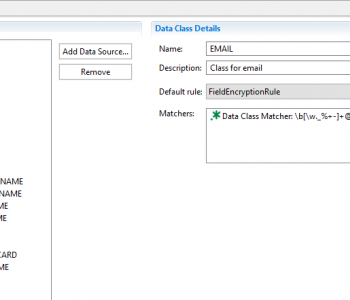
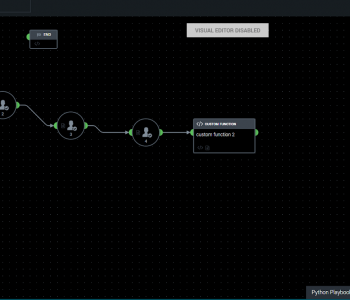
 Data Masking/Protection
Data Masking/Protection
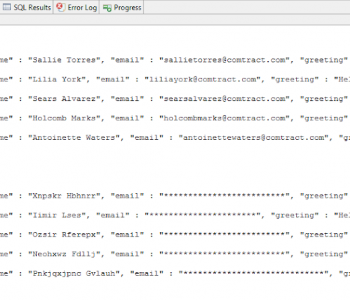
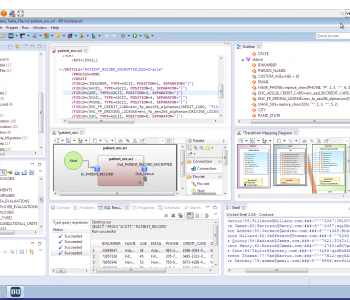
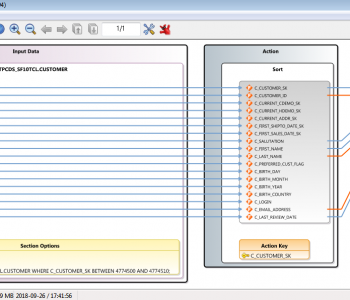
Connecting to, and Masking Data, in Salesforce
IRI Workbench users can connect to and manipulate the data in the underlying database in Salesforce using the JDBC and ODBC drivers from CData or Progress Software. Read More