 ETL
ETL
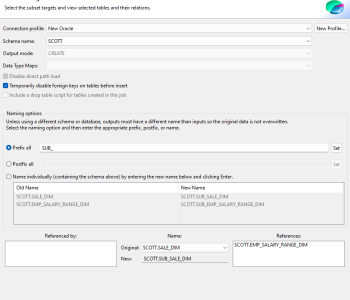
Creating a Voracity Flow from a Wizard (Part 2…
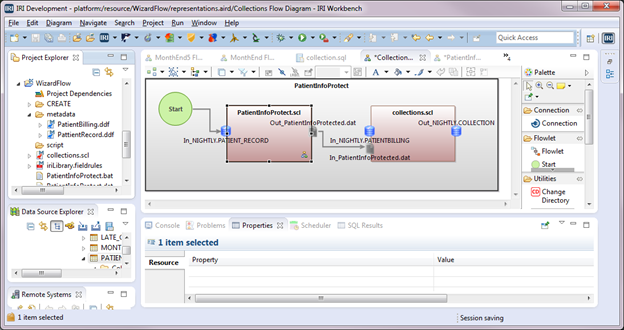
This is the second of two articles where we are creating an IRI Voracity ETL flow using new jobs wizards in the IRI Workbench GUI for Voracity, built on Eclipse. Read More
 ETL
ETL
This is the second of two articles where we are creating an IRI Voracity ETL flow using new jobs wizards in the IRI Workbench GUI for Voracity, built on Eclipse. Read More
 Data Masking/Protection
Data Masking/Protection
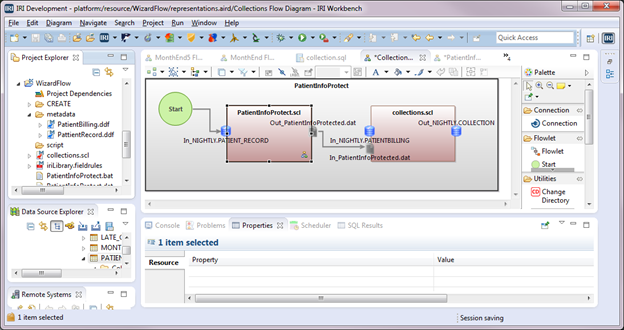
This is the first of two articles showing how to create and use job flows in the IRI Workbench GUI for Voracity. It follows two other series on creating flows automatically using new job wizards. Read More
 Data Masking/Protection
Data Masking/Protection
Editor’s Note: This article was writen in 2016. But since 2023, there are even more robust PII discovery capabilities for data in structured, semi-structured, and unstructured (RDB, NoSQL DB, file, document, and image) sources using IRI DarkShield, including Named Entity Recognition (NER) model matchers. Read More
 Data Masking/Protection
Data Masking/Protection
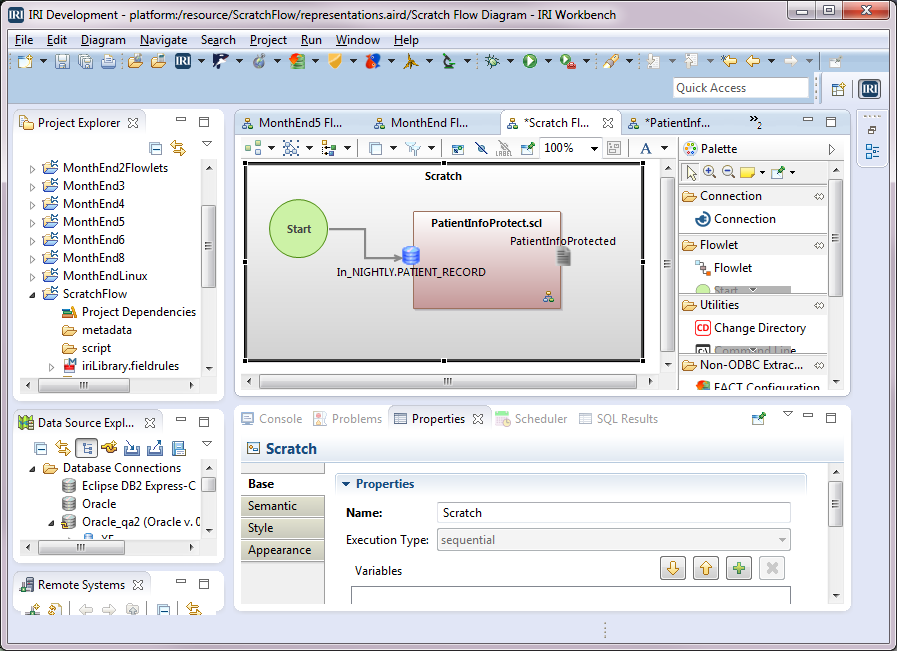
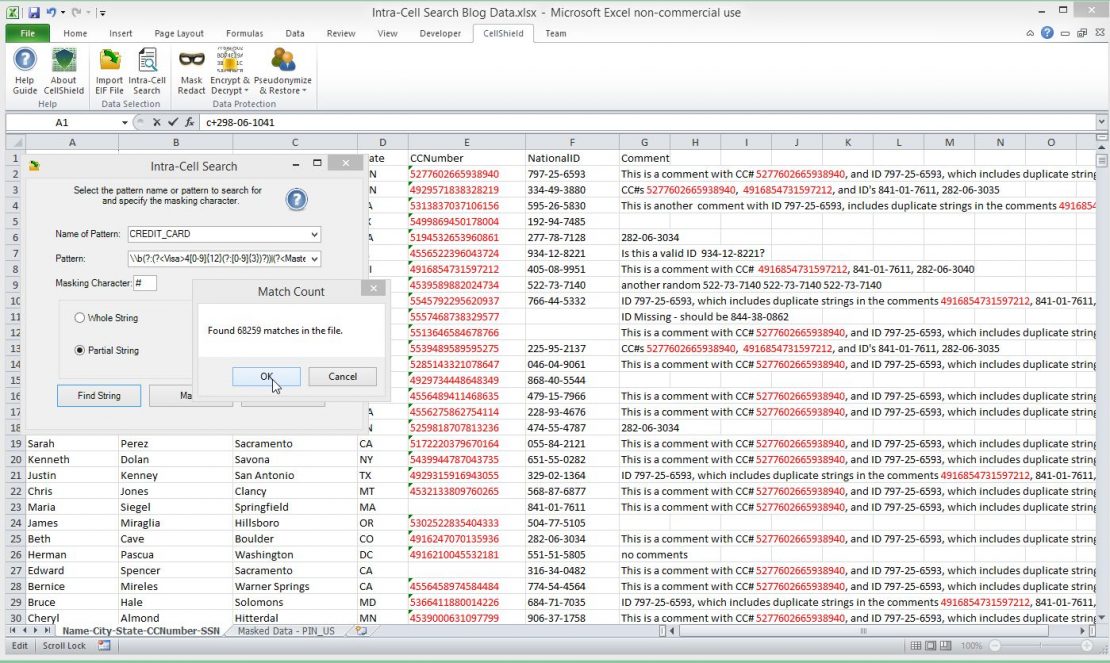
IRI CellShield™ Enterprise Edition now offers an Intra-Cell Search feature that finds and protects sensitive data in unstructured cell contents with masking, encryption, or pseudonymization. Just as with full-cell values, you can now identify and mask the ‘floating’ sensitive data in Microsoft Excel® spreadsheets with only a few mouse clicks. Read More
 Data Masking/Protection
Data Masking/Protection
Once a database exceeds a certain size, it becomes expensive — and risky from a security perspective — to provide full-size copies for development, testing, and training. Read More
 Big Data
Big Data
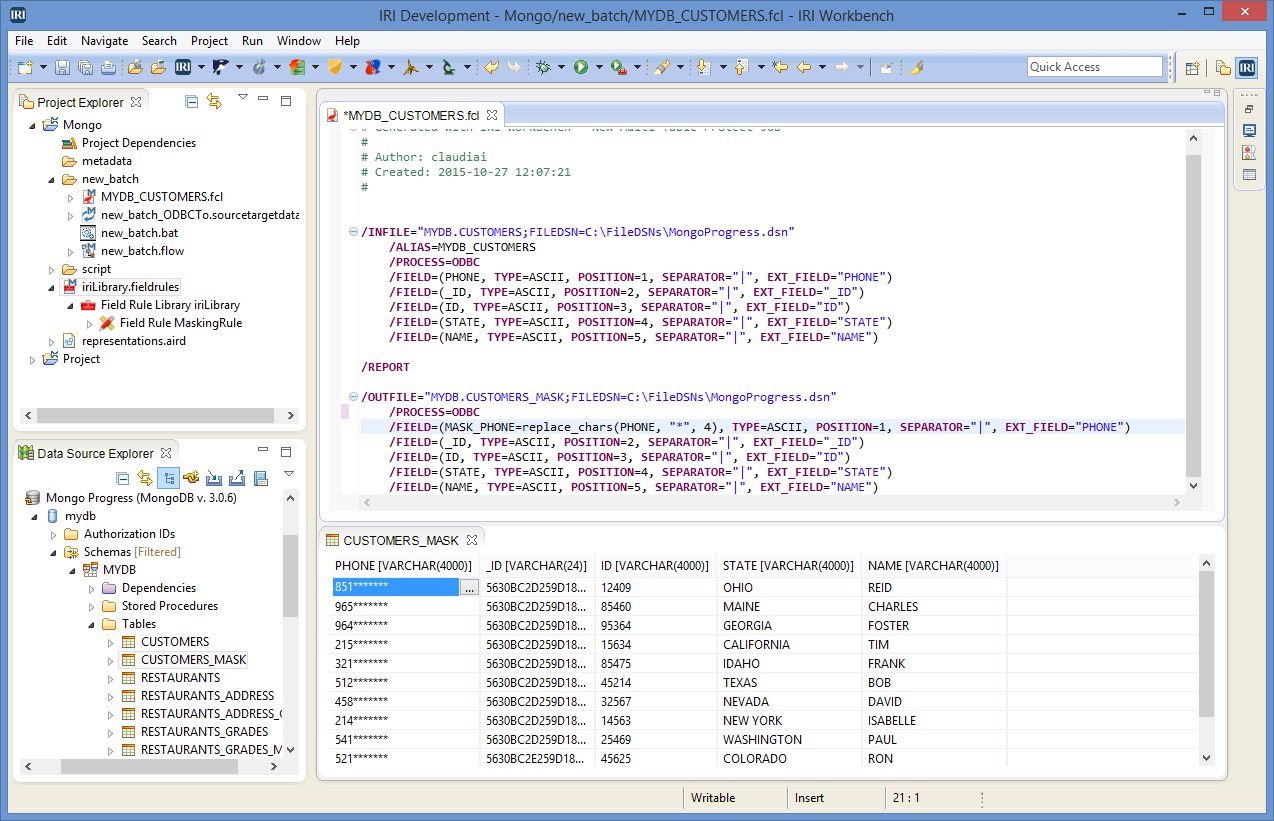
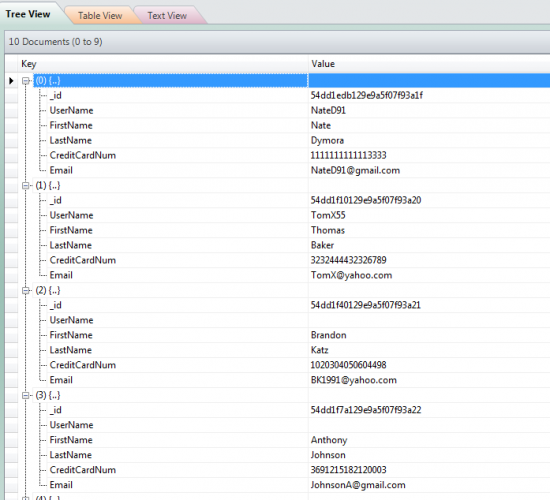
Note: This example demonstrates a more direct method of using IRI FieldShield or IRI Voracity to statically mask PII within structured MongoDB collections. Our older how-to-article on indirect data masking of MongoDB through export/mask/import from 2015 is here, and a newer method through MongoDB’s native driver support in CoSort v10 from 2018 is here. Read More
 Data Quality (DQ)
Data Quality (DQ)
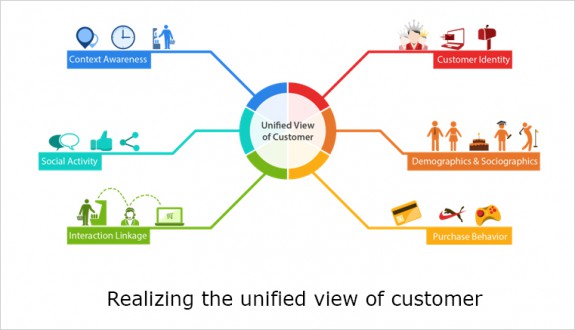
Customers drive business, and they want to be understood and valued. That starts with getting their (only) name right, and having an accurate view of their transaction history, preferences, and related information. Read More
 Data Masking/Protection
Data Masking/Protection
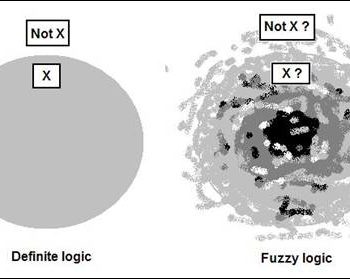
IRI is now also delivering fuzzy search functions, both in its free database and flat-file profiling tools, and as available field-function libraries in IRI CoSort, FieldShield, and Voracity to augment data quality, security, and MDM capabilities. Read More
 Big Data
Big Data
Editors Note: This example demonstrates our earliest, least direct (though still available) method of using IRI FieldShield for NoSQL database protection; i.e., for MongoDB data masking. Read More
 Business Intelligence (BI)
Business Intelligence (BI)
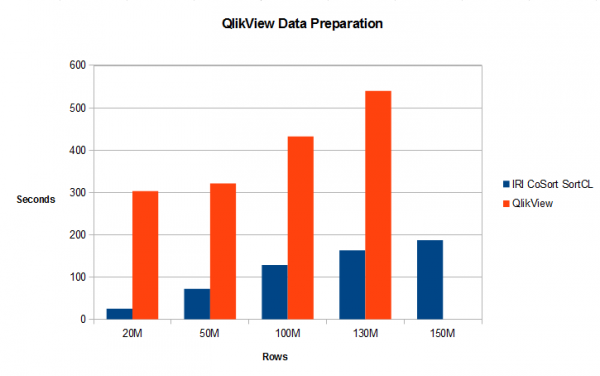
Introduction: As with multiple BI platforms discussed throughout this section of the IRI blog site, this article analyzes the relative data preparation performance (and benefit) of using its external data wrangling engine – via the IRI CoSort product or Voracity platform — with QlikView when ‘big data’ sources are involved. Read More